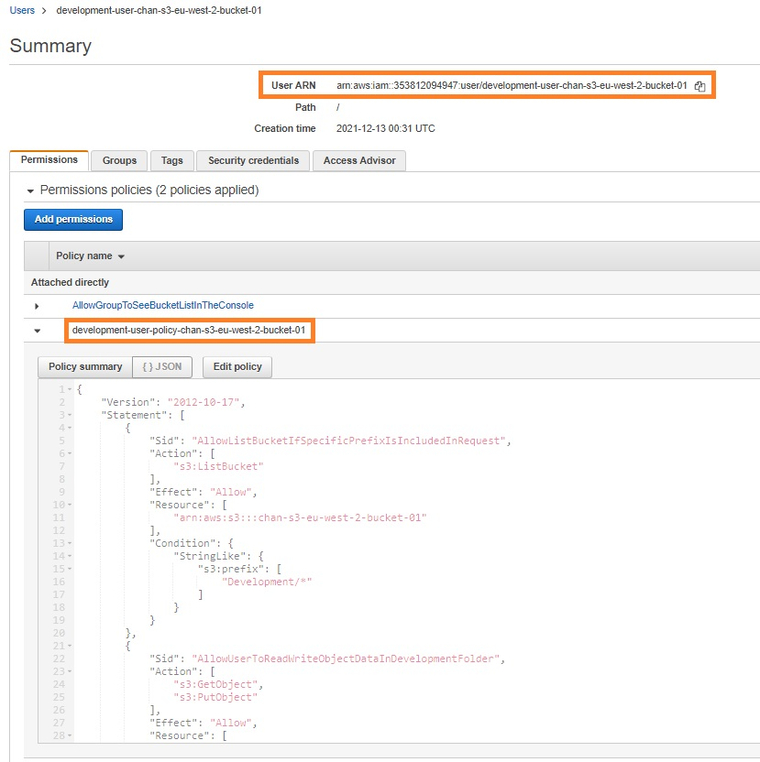
IAM makes it easier for you to manage permissions for AWS services accessing your resources | AWS Security Blog

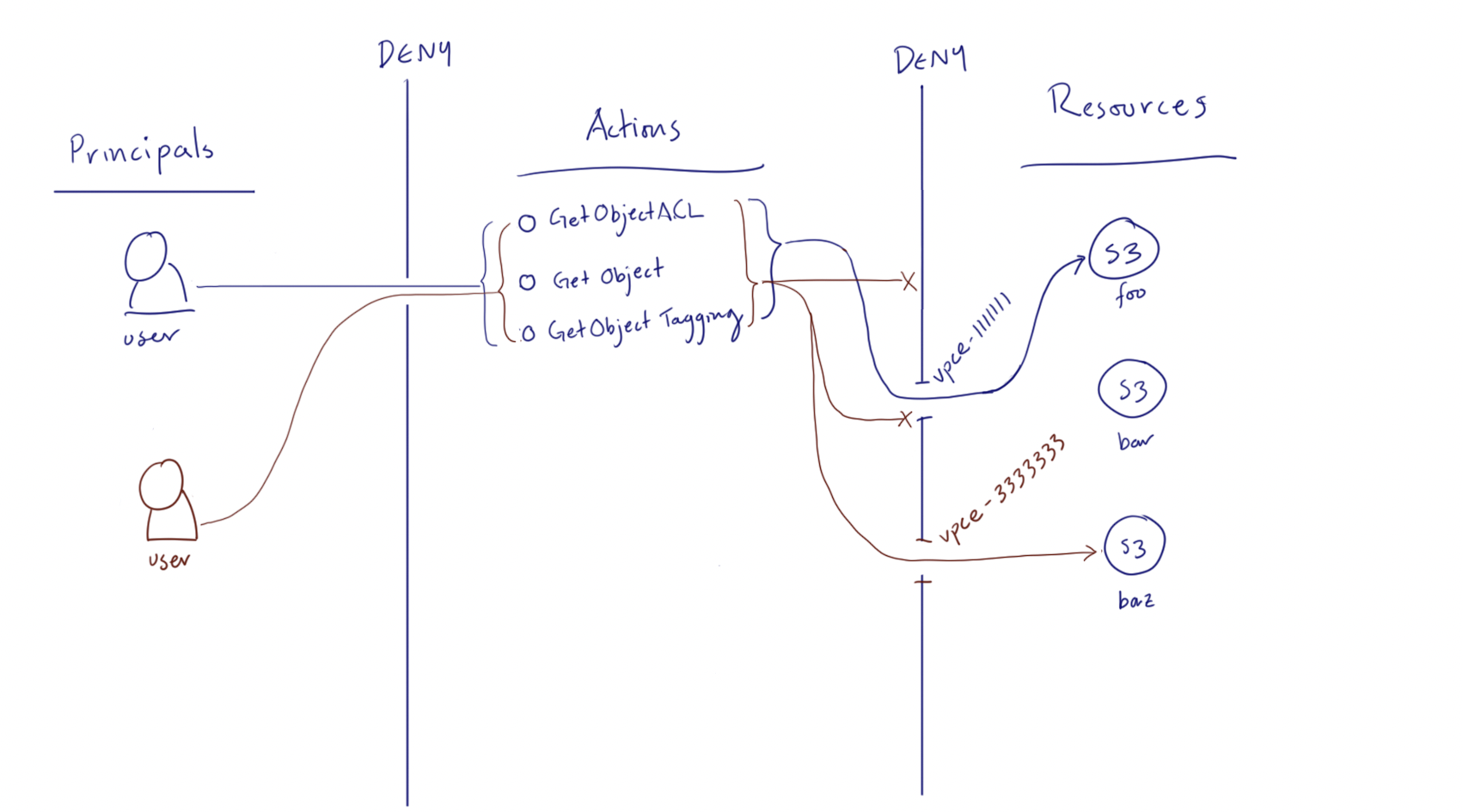
How do I configure an S3 bucket policy to deny all actions that don't meet multiple conditions? - YouTube

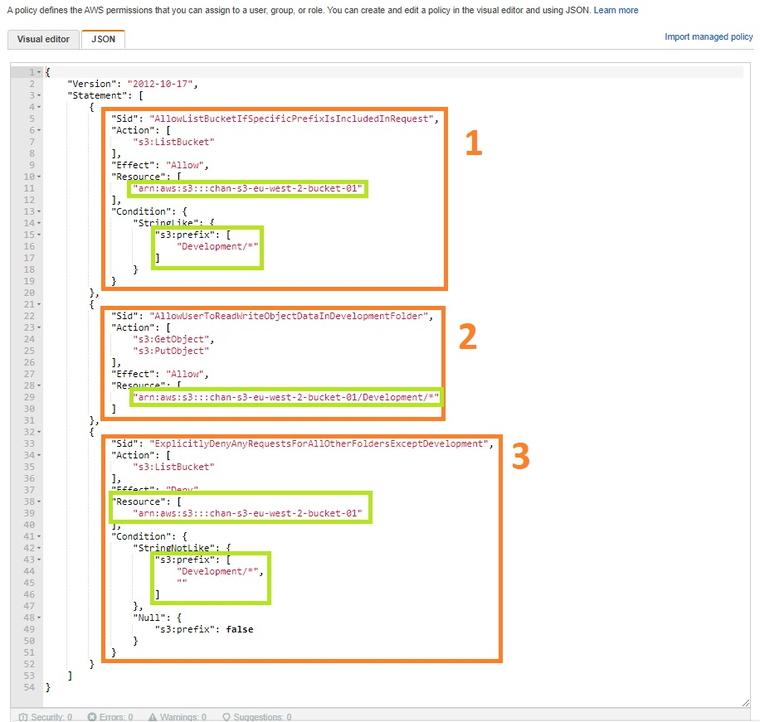
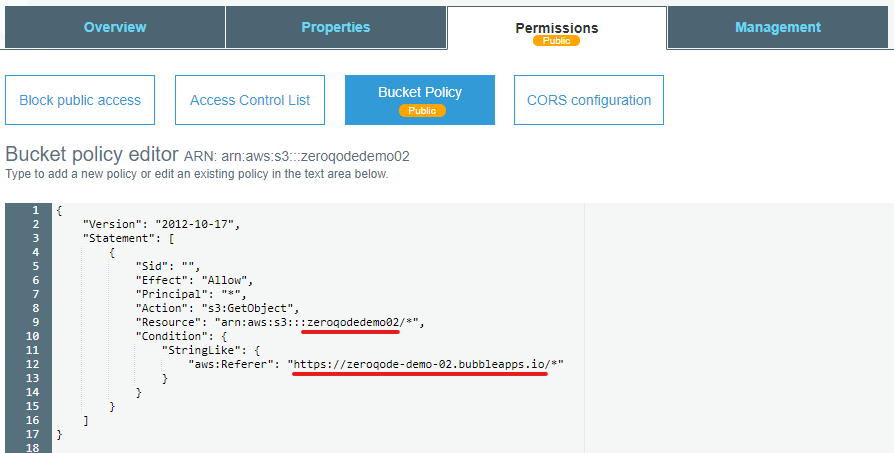
How to Use Bucket Policies and Apply Defense-in-Depth to Help Secure Your Amazon S3 Data | AWS Security Blog

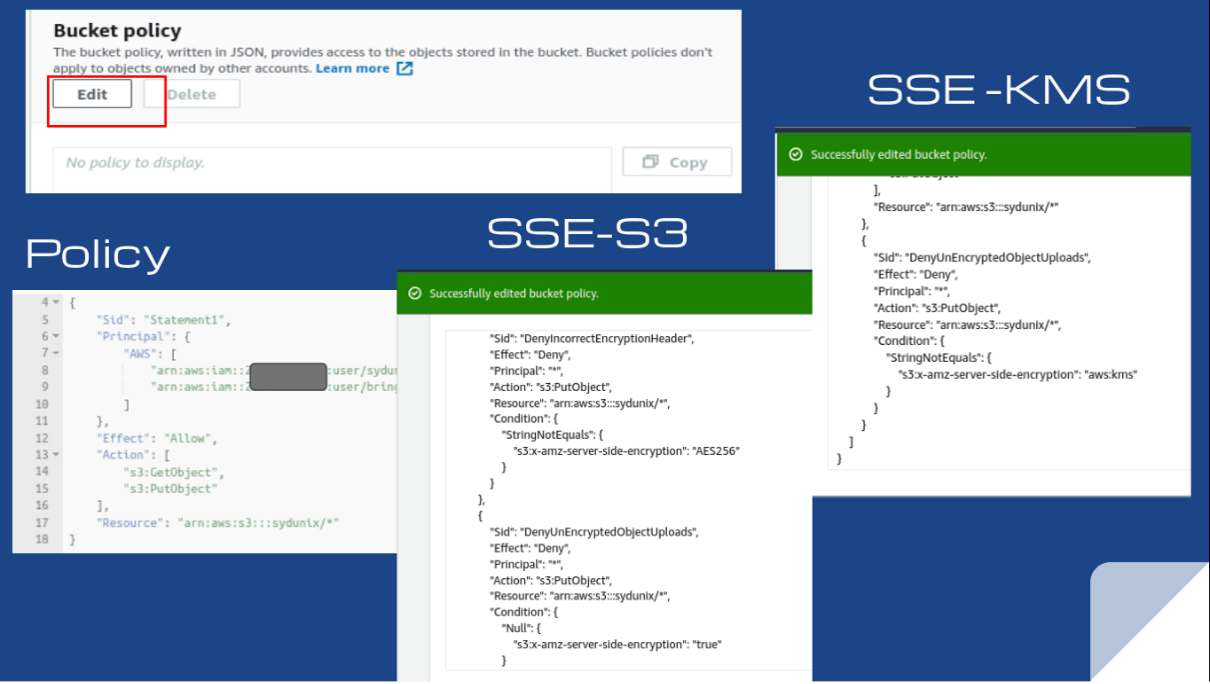
Sample S3 Bucket Policies. [Allowing only SSE-KMS based encrypted… | by Crishantha Nanayakkara | Medium
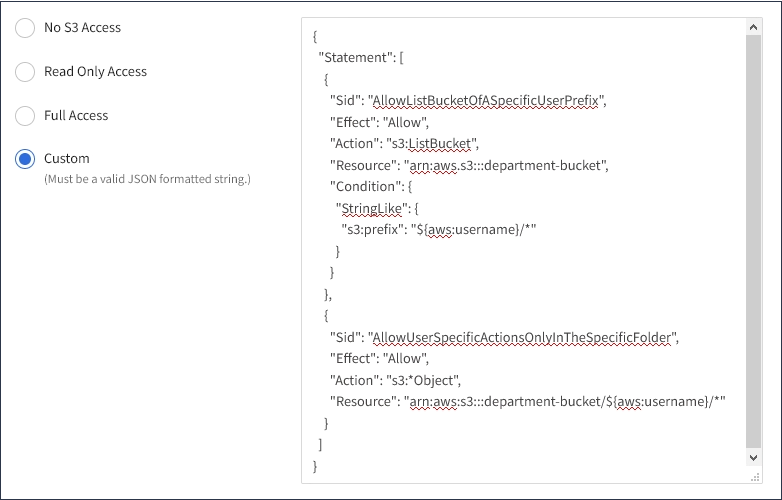
Lab Guide: Using S3 Bucket Policies and Conditions to Restrict Specific Permissions – Cloud Academy Help Center
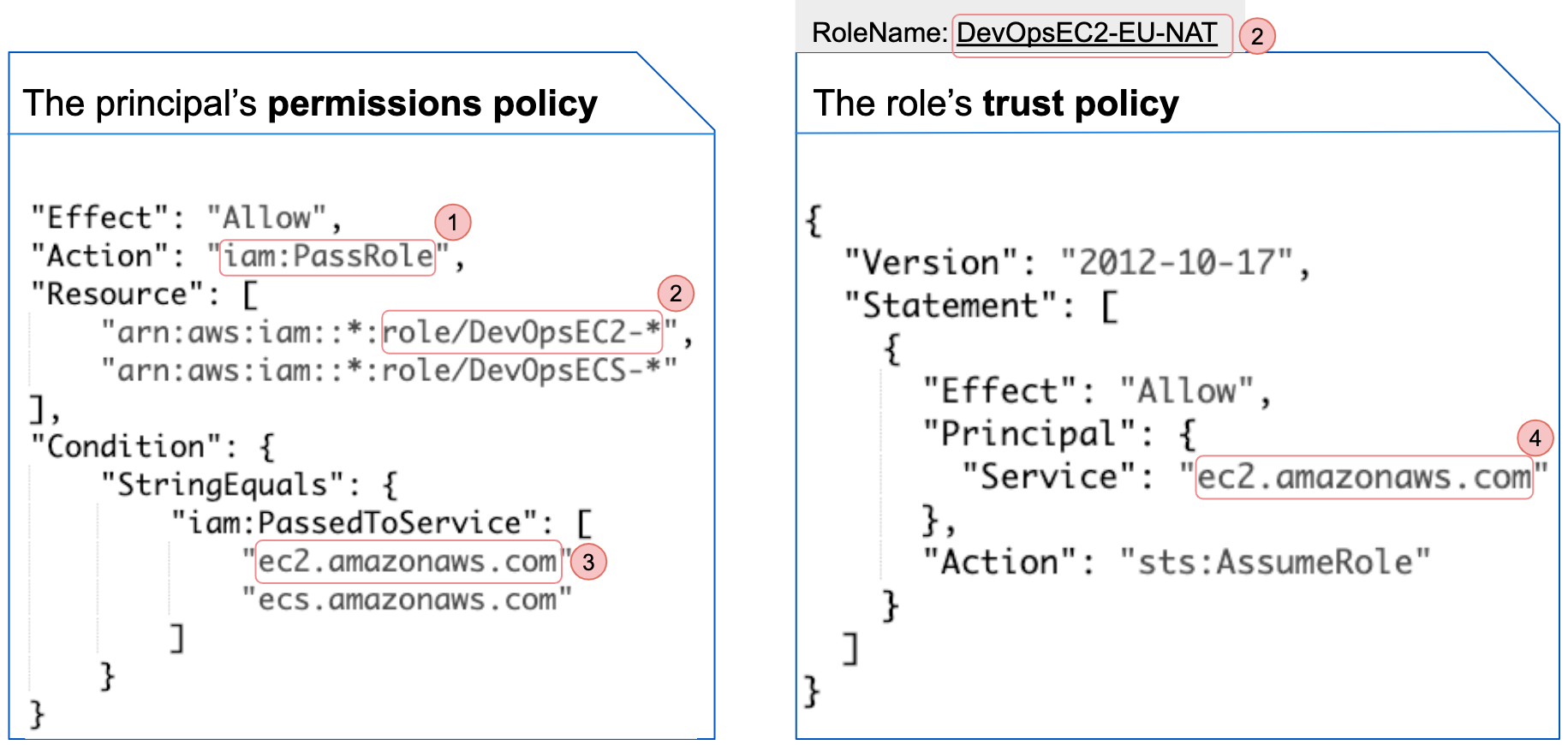
Unit 42 Cloud Threat Report: Misconfigured IAM Roles Lead to Thousands of Compromised Cloud Workloads
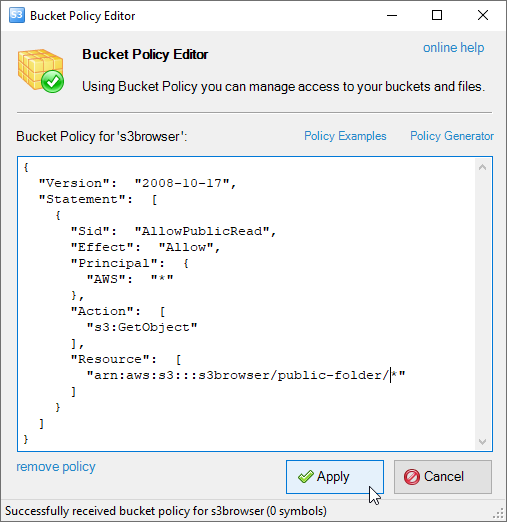
Amazon S3 Bucket Policies. How to configure Amazon S3 Bucket Policies. Examples of Bucket Policies. How to apply Amazon S3 Buckets Policies. View, Edit, Delete Amazon S3 Bucket Policies.

Sample S3 Bucket Policies. [Allowing only SSE-KMS based encrypted… | by Crishantha Nanayakkara | Medium